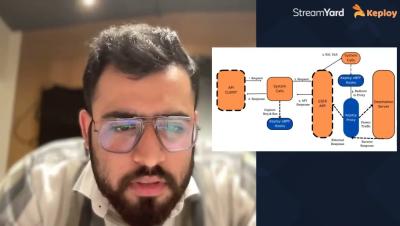
Exploring Various Protocols : Http To Databases
Ever wondered about the behind-the-scenes when you connect to a database, make an HTTP request, or check your Gmail? How does a server distinguish your legitimate device from an unauthorised interloper?